Mercor, the AI-powered recruitment platform that connects skilled workers with top AI companies, has confirmed a data security incident affecting thousands of users.
In an email sent to affected users this week, the three-year-old U.S.-based startup said the breach stemmed from a supply chain attack involving LiteLLM, a widely used open-source library.
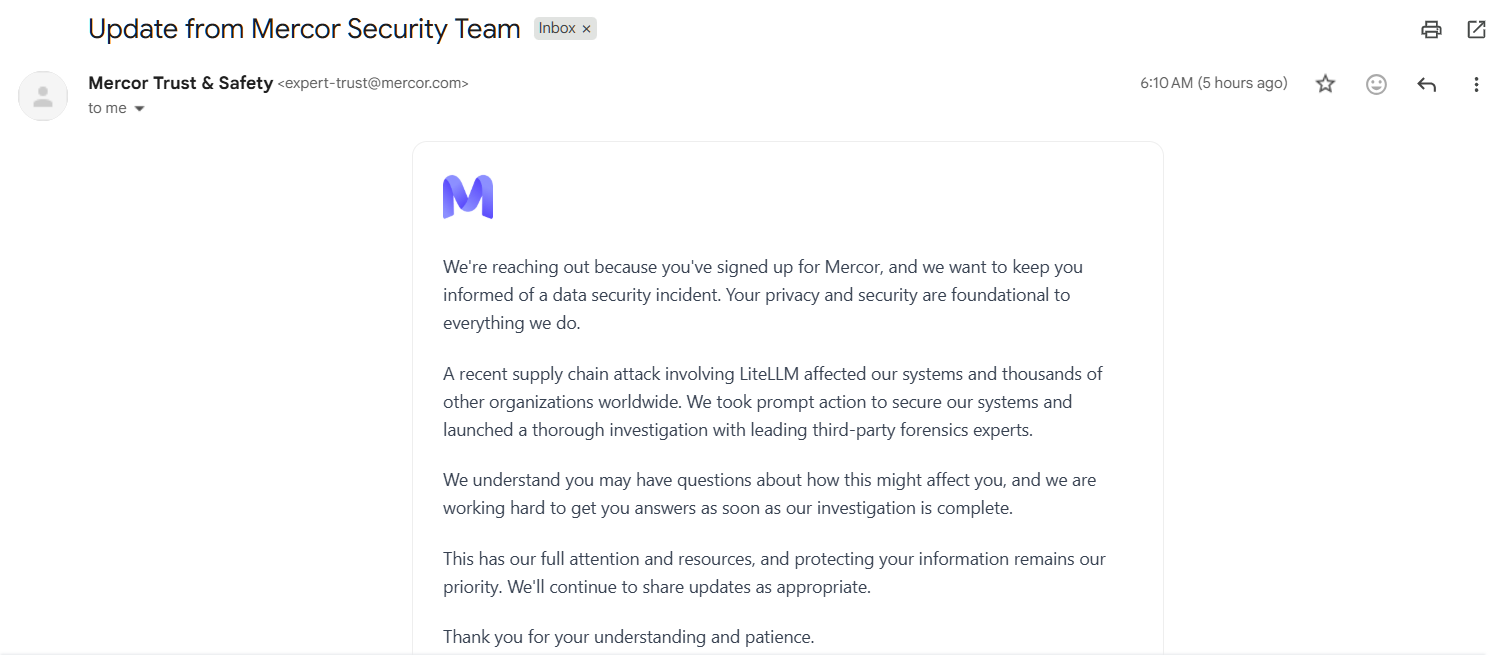
“A recent supply chain attack involving LiteLLM affected our systems and thousands of other organizations worldwide,” the company said. “We took prompt action to secure our systems and launched a thorough investigation with leading third-party forensics experts.”
For tech professionals on the platform, the breach potentially exposes sensitive data submitted during sign-up or contract work, including personal details, professional credentials, and possibly interactions with Mercor’s AI systems.
Mercor later confirmed the incident in a statement to Fortune, noting that it was among the companies affected by the LiteLLM compromise. The library, used by developers to connect applications to AI services from companies like OpenAI and Anthropic, is downloaded millions of times daily, according to cybersecurity firm Snyk, making it a high-value target for attackers.
The attack has been linked to a hacking group known as TeamPCP, which inserted malicious code into LiteLLM designed to harvest credentials and spread rapidly across systems. Although the code was identified and removed within hours, it had already impacted multiple organizations.
Mercor described itself as “one of thousands of companies” affected. A company spokesperson, Heidi Hagberg, said Mercor “moved promptly” to contain the incident and has launched an ongoing third-party forensic investigation.
“The privacy and security of our customers and contractors is foundational to everything we do at Mercor,” Hagberg said. “We will continue to communicate with our customers and contractors directly as appropriate and devote the resources necessary to resolving the matter as soon as possible.”
However, the situation may extend beyond the initial breach. The extortion-focused hacking group Lapsus$ has claimed it separately targeted Mercor and accessed its data. The group has reportedly published samples of allegedly stolen information, including what appears to be Slack data, internal ticketing records, and videos said to show conversations between Mercor’s AI systems and contractors.
Lapsus$ claims to have obtained as much as four terabytes of data, including source code and database records. Mercor has not publicly responded to these claims.
Security researchers at Wiz, quoted by Infosecurity Magazine, say TeamPCP may have begun collaborating with Lapsus$ and other ransomware-focused groups, raising concerns that the attack could be part of a broader, coordinated campaign. Cybernews also reported that TeamPCP has expressed intentions to partner with extortion groups to target affected companies at scale.
The incident positions Mercor as a potential early example of a wider wave of attacks linked to the LiteLLM supply chain compromise.
For now, the company has assured users that the situation is a priority.
“This has our full attention and resources, and protecting your information remains our priority,” Mercor said.
LiteLLM Supply Chain Attack Exposes Developer Credentials Through Malicious PyPI Versions
The compromised versions — 1.82.7 and 1.82.8 — included a hidden .pth file named litellm_init.pth.